Pegasus surveillance
On January 28, the New York Times published an article extensively detailing how Pegasus, a spyware developed by Israel-based NSO Group, has been used as a tool to firm up Israel’s interests across the globe.
Claims of the investigative article:
 Impact of Pegasus in India
Impact of Pegasus in India
- Israel got countries that had historically been against it on the Palestine issue to switch sides by offering this powerful spyware that can be deployed not only against drug traffickers and terrorists, but also against opposition activists and prying journalists.
- The tool is cited as one of the reasons why the Abraham accords between Israel and its neighbouring Arab countries fell into place and won the blessing of Saudi Arabia.
- Pegasus was part of a $2-billion “package of sophisticated weapons and intelligence gear” transaction between India and Israel after Narendra Modi became the first Indian Prime Minister to visit Israel. It was after this deal that India changed its historically pro-Palestine stance and voted in Israel’s favour in 2019 “at the U.N.’s Economic and Social Council to deny observer status to a Palestinian human rights organization.”
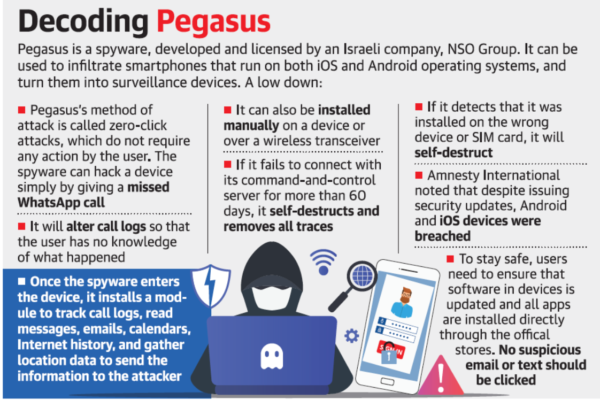
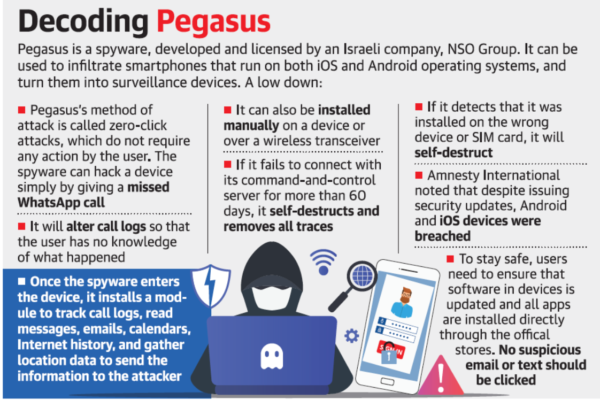
- Capabilities of the spyware: It can not only mop up information stored on phones such as photos and contacts, but also activate a phone’s cameras and microphones to turn it into a spying device without the owner’s knowledge.
- Mechanism:
-
-
- The earliest avatars of Pegasus used spear phishing to enter phones, utilising a message designed to entice the target to click on a malicious link.
- However, it evolved into “zero-click” attacks with the phones being infected without any action from the target individual.
-
-
- Detection of the Pegasus system for the first time:
- In 2019, WhatsApp released a statement saying that Pegasus could enter phones via calls made on the platform, even if they were not attended.
- Pegasus used several such “exploits”, or weaknesses, to enter Android and Apple phones; and many of these exploits were reported “zero day”, which means even the device manufacturers were unaware of these weaknesses.
- Multiple channels: Pegasus can also be delivered over the air from a nearby wireless transmitter, or manually inserted if the target phone is physically available. Once inside the phone, Pegasus seeks “root privileges”, a high level of control over the phone that enables the spyware to establish communications with its controllers through an anonymised network of internet addresses and servers.
- It can then start transmitting any data stored on the phone to its command-and-control centres.
- Misuse of the Pegasus system(according to the article):
- It was reportedly used to entrap and murder Jamal Khashoggi, a critic of the Saudi Arabian Crown Prince Mohammed Bin Salman.
- It was used by UAE and Mexico and others against government critics alongside drug traffickers.
- The U.S.’s FBI also reportedly tested it out, though it was not deployed in the country.
- Accessibility of the system: Since Pegasus is graded as a cyberweapon and can be sold only to aauthorized government entities as per Israeli law, most reports have suggested that the governments in these countries are the clients.
- Detection of the Pegasus system for the first time:
 Impact of Pegasus in India
Impact of Pegasus in India
-
- It was used to tap The Wire in India, The Guardian in the U.K., and The Washington Post in the U.S. said that in India, at least 40 journalists, Cabinet Ministers, and holders of constitutional positions were possibly subjected to surveillance using Pegasus.
- The reports were based on a database of about 50,000 phone numbers accessed by the Paris-based non-profit Forbidden Stories and Amnesty International.
- These numbers were reported of interest to clients of the NSO Group, primarily from 10 countries.
- According to The Guardian, Amnesty International’s Security Lab tested 67 of the phones linked to the Indian numbers in the database and found that “23 were successfully infected and 14 showed signs of attempted penetration”.
-
- The Indian government has so far neither confirmed nor denied that it has deployed Pegasus for any operation.
- In the wake of the Pegasus Project revelations, several petitions were filed with the Supreme Court alleging that the Government has indulged in mass surveillance in an attempt to muzzle free speech and to chill dissent. In this context, the Supreme Court asked the Centre to file a detailed affidavit regarding the use of Pegasus.
- However, the Centre refused to comply, arguing that such a public affidavit would compromise national security.
- Following this, the Supreme Court on October 27, 2021 appointed an expert panel monitored by retired Supreme Court judge Justice R.V. Raveendran to probe and file a report on the spying allegations. The panel is yet to file the report.
-
- In PUCL vs Union of India case, 1996, the Supreme Court said telephonic conversations are covered by the right to privacy, which can be breached only if there are established procedures.
- In the K.S. Puttaswamy vs Union of India verdict of 2017, the Supreme Court further reiterated the need for oversight of surveillance, stating that it should be legally valid and serve a legitimate aim of the Government. The court also said the means adopted should be proportional to the need for surveillance, and there should be procedures to check any abuse of surveillance.
-
- Provisions of the Indian Telegraph Act, 1885 - Section 5(2) states that the Government can intercept a “message or class of messages” when it is “in the interests of the sovereignty and integrity of India, the security of the State, friendly relations with foreign states or public order or for preventing incitement to the commission of an offence”.
- Rule 419A of the Indian Telegraph Rules, 1951 mentions the Operational procedure:
- It was added to the Telegraph Rules in 2007 after the verdict in the PUCL vs Union of India case, 1996, in which the Supreme Court said telephonic conversations are covered by the right to privacy, which can be breached only if there are established procedures.
- Such surveillance needs the sanction of the Home Secretary at the Central or State level, but in “unavoidable circumstance” can be cleared by a Joint Secretary or officers above, if they have the Home Secretary’s authorisation.
- Section 69 of the Information Technology Act, 2000, which deals with electronic surveillance.
- It facilitates Government “interception or monitoring or decryption of any information through any computer resource” if it is in the interest of the “sovereignty or integrity of India, defence of India, security of the State, friendly relations with foreign States or public order” or for preventing or investigating any cognizable offence.
- Procedure for electronic surveillance as provided in Information Technology (Procedure and Safeguards for Interception, Monitoring and Decryption of Information) Rules, 2009.
- These rules are very broad and allow even the redirection of traffic to false websites or the planting of any device to acquire any information.
- Unauthorised access under Section 66 of the Information Technology Act: It prescribes punishment to anyone who gains unauthorised access and “downloads, copies or extracts any data”, or “introduces or causes to be introduced any computer contaminant or computer virus,” as laid down in Section 43.
Posted on 31-01-2022 • By Admin